Before coming to actual deployment, there are a few prerequisites you need to take care of:
- You must have an active Azure subscription.
- Log analytics workspace.
- To enable this service, you need contributor permissions to the subscription in which the workspace resides.
- To use this service, you need to have either contributor or reader role on the resource group to which workspace belongs.
- You can not use it in China or Germany regions.
Enable Azure Sentinel
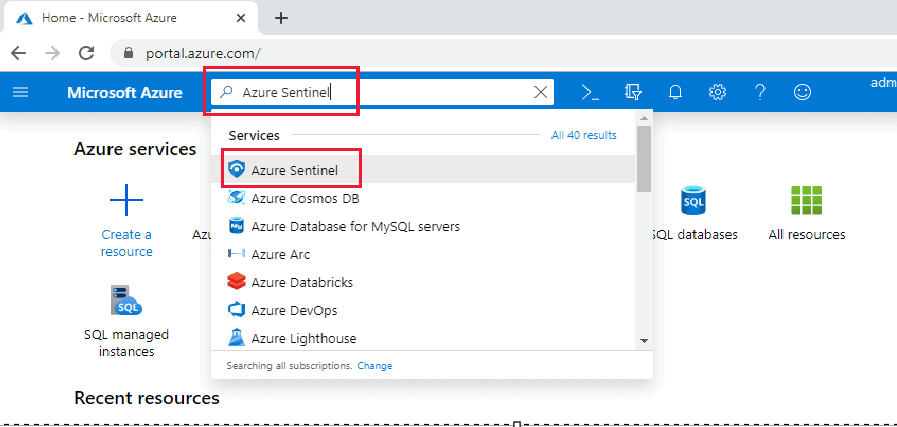
Sign in to the portal and Search and select Azure Sentinel:
Choose an existing workspace or create a new one. You can run sentinel on multiple workspaces, but the data is only stored in one of them.
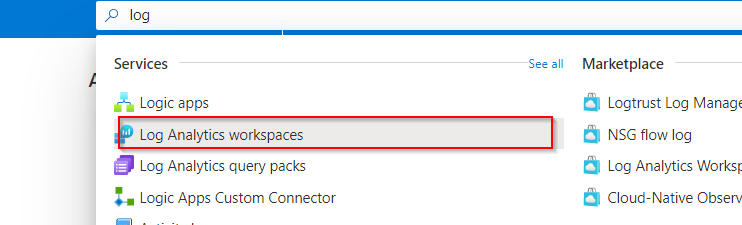
To create a workspace: In the Azure portal, in the Search resources, services, and docs text box at the top of the Azure portal page, type Log Analytics workspaces and press the Enter key.
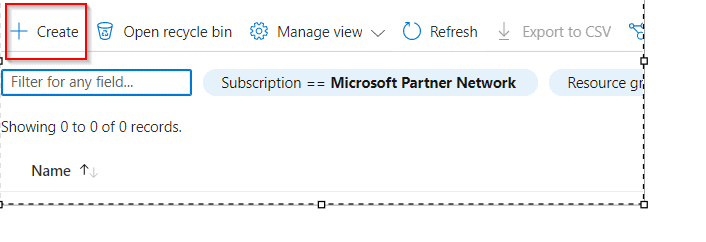
Create the log Analytics:
Connect Data Source
By connecting to the service and passing the events and logs to it, Azure Sentinel ingests data from services and apps. You can deploy the Log Analytics agent on both real and virtual machines, which collects logs and sends them to Azure Sentinel. It installs the Log Analytics agent on a Linux Syslog server for firewalls and proxies, from which the agent gathers log files and passes them to Azure Sentinel.
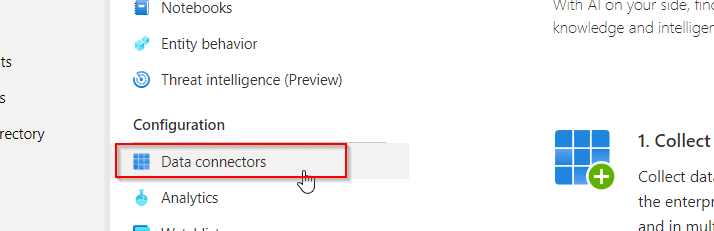
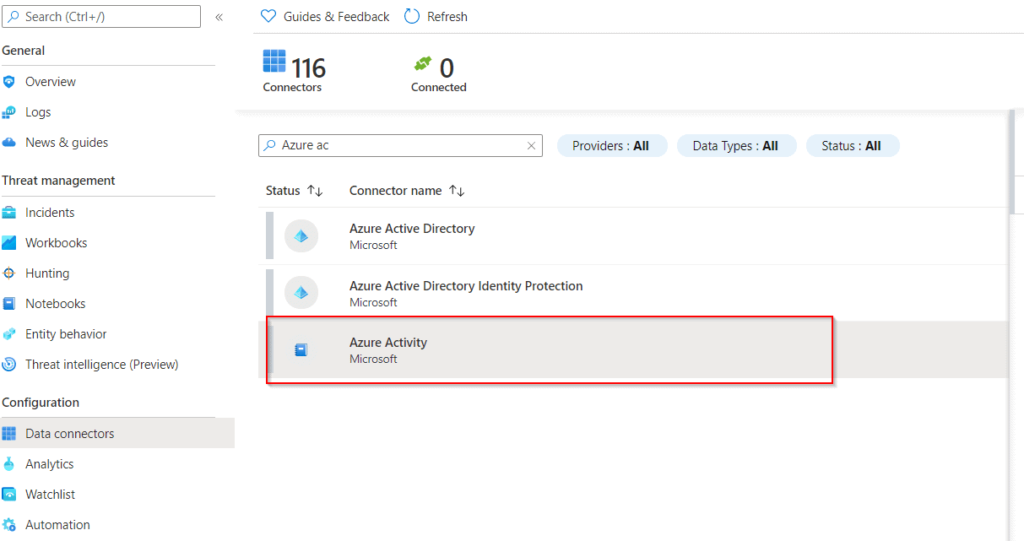
- Select Data connectors from the main menu. This brings up a gallery of data connectors.
- The gallery contains a list of all the data sources that you can use. Then click the Open connector page button after selecting a data source and install left hand side box.
- Furthermore, The connector page not only provides guidance on the initial setup process but also offers additional instructions that may be necessary
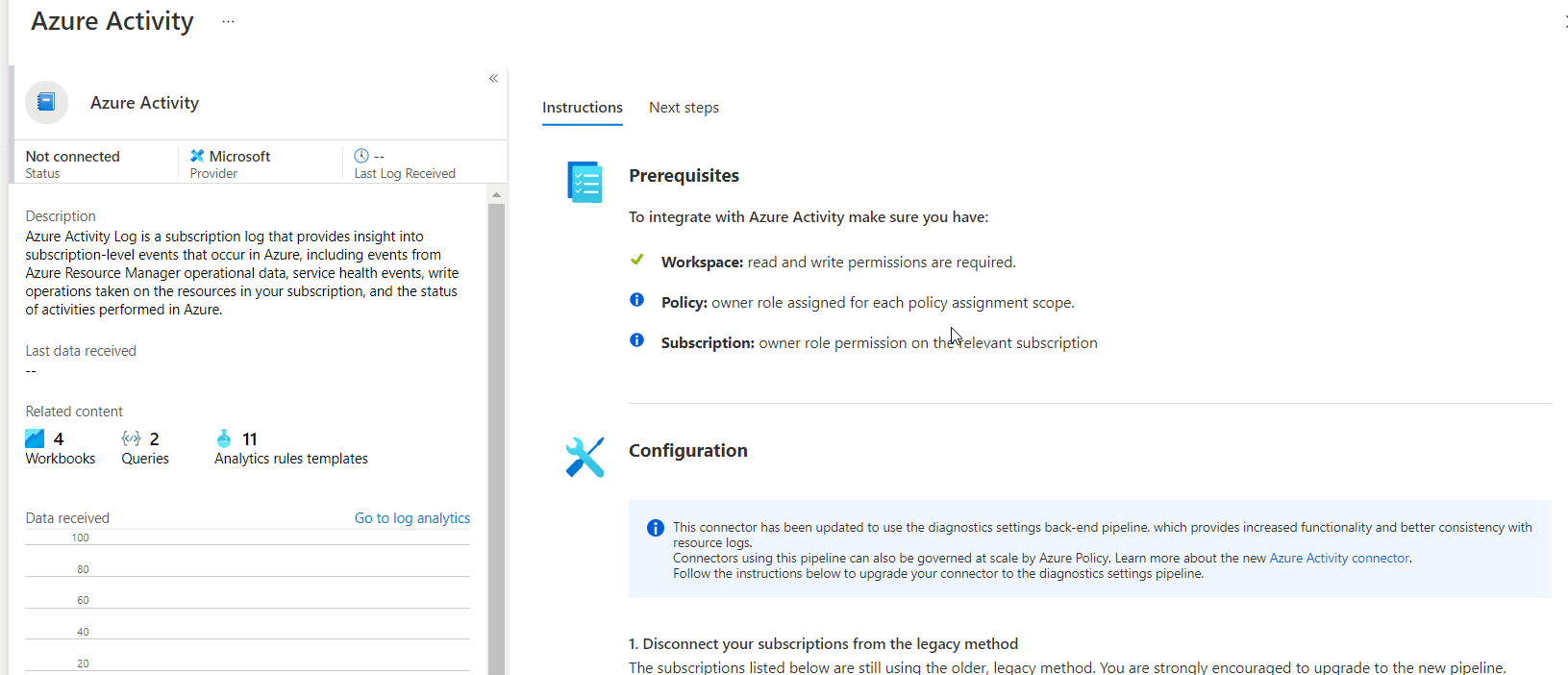
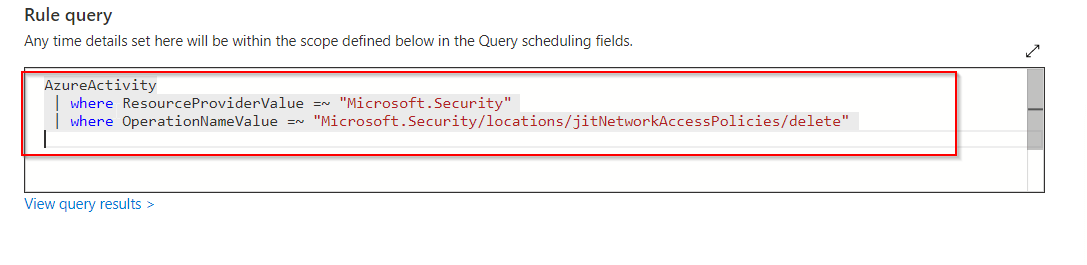
- The Next steps tab on the connection page displays the data connector’s built-in workbooks, example queries, and analytics rule templates. You can use them as-is or tweak them; either way, you’ll receive exciting insights into your data right away.
After you connect your data sources, your data begins to flood into Azure Sentinel and is ready for you to work with. To explore the data, you may browse the logs in the built-in workbooks and start generating queries in Log Analytics.

Conclusion:
Azure Sentinel is a cloud-native SIEM tool that has the features of both SIEM and SOAR solutions, and is a scalable solution for detecting, investigating, and responding to threats. It allows consumers to spot potential problems sooner. Machine learning is used to reduce hazards and detect anomalous activities. It is all about bringing everything we want to see together in order to reduce false positives and eliminate issues, which has historically been a difficult topic to solve.