Azure Sentinel is a critical component of an organisation’s cybersecurity strategy. By leveraging its advanced threat detection and response capabilities, comprehensive visibility, cost-effectiveness, and simplified management, organisations can enhance their security posture and effectively combat the evolving threat landscape. Embrace the power of Azure Sentinel to safeguard your organisation’s critical assets and stay one step ahead of cyber threats.
- Log Management and gathering data from across your enterprise.
- Enhanced Threat Detection.
- Puts together a Security Automation and Security Orchestration
- It automates repetitive tasks and an Incident Response.
- It integrates with other Azure services such as Azure AD, Microsoft Defender for Cloud , and Information Protection to provide a comprehensive security solution for an organization
- It allows users to create their own custom connectors to ingest data from any source and supports the use of APIs to integrate with third-party tools and services. Additionally, users can create custom workbooks and dashboards to visualize and analyze security data in ways that are relevant to their organization
LifeCycle :
The life of Azure sentinel starts with understanding what information is available to us, then how we are looking into it, followed by investigation when we see the evidence of things that may or may not be usual and finally responds to that unusual activity associated with that investigation.
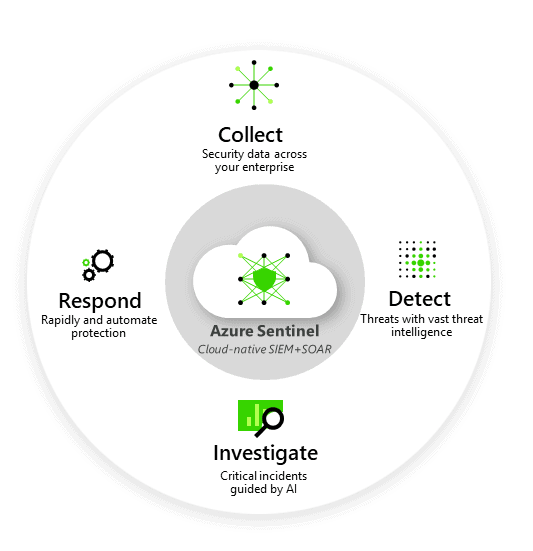
Undoubtedly, It is a complicated technology, but we have to understand why it is essential for an organization to consider deploying it. It is essential because of the elements in its lifecycle.
- When we talk about collect, we could reach out and get information from various systems, endpoints, devices, servers, workstations, mobile platforms, and our on-premise, cloud-based infrastructure, multi cloud-based infrastructure. With the help of connects, we can reach out to other clouds, integrate and pull the information using Azure Sentinel.
- We can detect millions of different events across that globe in real-time using artificial intelligence, machine learning, and advanced analytics capability.
- Not only detect but also investigate the information across that globe using artificial intelligence and machine learning.
- Microsoft looks at all sorts of information every day and tells us how to understand our system in the best possible way. If there is an issue, the system will know what action we have to take or how we have to respond to address the issue to minimize its impact potentially.
A playbook can help you automate and coordinate your threat response; it can integrate with other internal and external systems, and it can be set to execute automatically in response to certain warnings or incidents prompted by analytics or automation rules, respectively. It can also be run manually from the incidents page in response to alerts.
Features of Azure Sentinel :
Azure Sentinel is a cloud-native security information and event management (SIEM) and security orchestration, automation, and response (SOAR) solution that helps you collect data from a variety of sources, analyze it for threats, and respond to incidents quickly and effectively.
There are many SIEM tools within the platform. But still, this is designed to take care of even a tiny possibility of a security loophole and ensure a secure environment.
It offers a wide range of features and components that can help you improve your security posture and reduce your risk of a data breach and we will discuss few major ones.
Security Data Collection and Integration
It allows organizations to collect security data from various sources, including logs, events, and alerts generated by cloud resources, on-premises infrastructure, applications, devices, and third-party solutions. It provides out-of-the-box connectors for Microsoft services like Microsoft Threat Protection and Microsoft 365 solutions (Office 365, Azure AD, Azure ATP, Microsoft Cloud App Security). Moreover, it supports custom data connectors, enabling integration with a wide range of third-party solutions.
Threat Detection and Hunting
Azure Sentinel employs advanced analytics and machine learning capabilities to detect and identify potential security threats and anomalies in real-time. It utilises built-in analytics rules, anomaly detection, behaviour analysis, and threat intelligence to detect malicious activities, suspicious behaviours, and emerging threats. Additionally, it enables proactive threat hunting by empowering security analysts to explore and investigate security incidents and conduct in-depth analysis to identify hidden threats
Security Orchestration, Automation, and Response (SOAR)
Azure Sentinel functions as a SOAR solution, allowing organizations to automate and streamline security operations. It provides automation playbooks and workflows to execute predefined actions, such as alert enrichment, incident triaging, and response orchestration. By automating repetitive tasks, it accelerates incident response and reduces manual effort, enabling security teams to focus on critical security activities.
Incident Management and Investigation
Azure Sentinel offers a unified incident management console that allows security analysts to track, prioritise, and manage security incidents from a centralised location. It provides rich visualization capabilities, including interactive workbooks and dashboards, to facilitate in-depth investigation and analysis of security events. Security analysts can collaborate, annotate, and share findings within the platform, enhancing the efficiency and effectiveness of incident response.
It encompasses a comprehensive set of features and components that enable organizations to collect, analyze, and respond to security incidents effectively. By leveraging its capabilities for security data collection, threat detection and hunting, incident management, automation.
It offers many features, and for all of the features, AI is the key. And With the use of AI, Sentinel shoots any suspicious activities within your cloud services.
Components of Azure Sentinel:
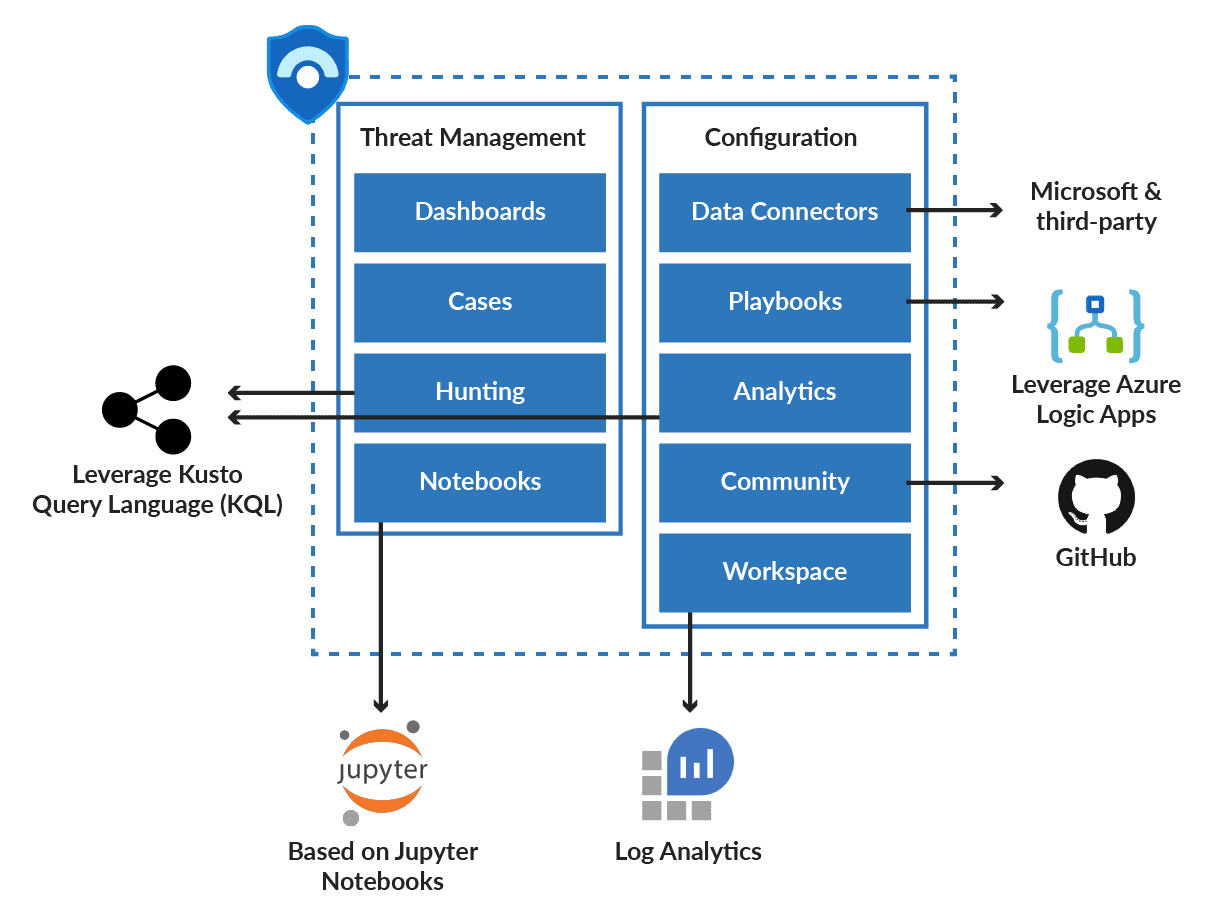
There are nine significant Components :
- Dashboards: It provides a visualization of data gathered from different sources, enabling the security team to look into events generated by those services.
- Cases: The collection of evidence related to the specific investigation is known as cases. It can contain more than one alert based on analytics defined.
- Hunting: As the name suggests, it is responsible for performing proactive threat analysis across the environment.
- Notebooks: Integrates with Jupyter Notebook, Sentinel provides a lot of scope of using libraries and modules for ML, visualization, etc.
- Data Connectors: Built-in connectors are available to facilitate data from Microsoft products and partners.
- Playbooks: It is like a guide that contains a collection of procedures to execute in response to an alert triggered by the sentinel.
- Analytics: It enables the users to create custom alerts using KQL( Kusto Query Language).
- Community: The community page contains sample queries for hunting, playbooks, and other stuff. It’s a GitHub-based Azure Sentinel page that has different data sources.
- Workspace: Log Analytics workspace or Workspace is a container that consists of data and configured information. Sentinel uses it to store data collected from different sources.